Partner POV | Identity Protection Innovations for Entra ID and Privileged Access
In this article
This article was written and contributed to our partner, CrowdStrike.
In the critical and constantly evolving identity security space, organizations are focused on three essential needs:
- Understanding identity posture: Visualizing and prioritizing risks associated with endpoints, applications and data as part of establishing baselines for user behavior.
- Proactive threat prevention: Mitigating known risks and remediating anomalies by blocking unacceptable activities and distinguishing between anomalous and malicious behavior.
- Effective threat detection and response: Once risks are identified and preventative controls are in place, organizations must detect and respond to any threats that bypass initial defenses — including CVE-based detections, unresolved anomalies and hybrid response capabilities.
While identity security disciplines like identity security posture management (ISPM), identity threat detection and response (ITDR) and privileged access management (PAM) address various aspects of these needs, none offer a complete solution. Today's adversaries are working to exploit the gaps between these disparate systems, and organizations are attempting to keep pace by collecting logs from various tools into a centralized SIEM for behavior analysis. Unfortunately, this approach is clunky and increasingly ineffective against modern adversaries.
This is where CrowdStrike Falcon® Identity Protection comes in. We provide a comprehensive, unified solution that meets all three needs. At Fal.Con 2024, we're excited to announce new innovations to help our customers address these challenges more effectively and efficiently: just-in-time access for privileged actions and real-time identity protection for Entra ID.
Real-Time Identity Protection for Entra ID
As more organizations rely on cloud-based identity providers like Microsoft Entra ID, adversaries are sharpening their focus on these vital systems. Threat actors are deploying increasingly sophisticated tactics, ranging from password spraying to advanced phishing attacks, to exploit misconfigurations and bypass weak multifactor authentication (MFA) processes.
Falcon Identity Protection delivers real-time threat prevention for Microsoft Entra ID, stopping threats before they strike. Powered by advanced user behavior analytics and risk-based access decisions, Falcon Identity Protection operates inline with every Entra ID authentication flow to stop adversaries in their tracks, block unauthorized devices and prevent identity-based attacks. It leverages the CrowdStrike Falcon® platform to assess user risk and device trust, as well as third-party sources like Intune and Entra ID. This enables real-time decisions to grant, block or enforce conditional access, ensuring your organization stays secure.
With these new innovations, CrowdStrike delivers key benefits for Entra ID protection:
- Real-time threat prevention: By sitting inline with Entra ID authentication flows, Falcon Identity Protection prevents identity-based attacks before they start.
- Dynamic access decisions: The Falcon platform enables accurate, real-time access decisions based on dynamic risk context and Falcon Zero Trust Assessment (ZTA) scores, ensuring only trusted users gain access,
- Hybrid risk-based conditional access: As this integration is based on the OpenID connect standard, Falcon Identity Protection can now enforce security controls across on-premises Active Directory and Entra ID. In the future, we can extend to other cloud-based identity providers to block unauthorized access or inject MFA based on threat level.
How It Works: Real-Time Protection at the Core
Falcon Identity Protection integrates seamlessly with Microsoft Entra ID through the external authentication method (EAM). By combining CrowdStrike's threat intelligence with Falcon risk scores and device trust data, organizations can make dynamic, real-time access decisions to prevent attacks before they happen. Our unified identity security and endpoint protection enable checks on Falcon sensor installation, user risk scores and more, ensuring only trusted users and devices can access sensitive resources.
Configuration

The new integration is powered by a cloud access trigger in the Falcon Identity Protection policy, allowing teams to configure behavioral rules with user, device, risk and IP reputation conditions.
Falcon Check
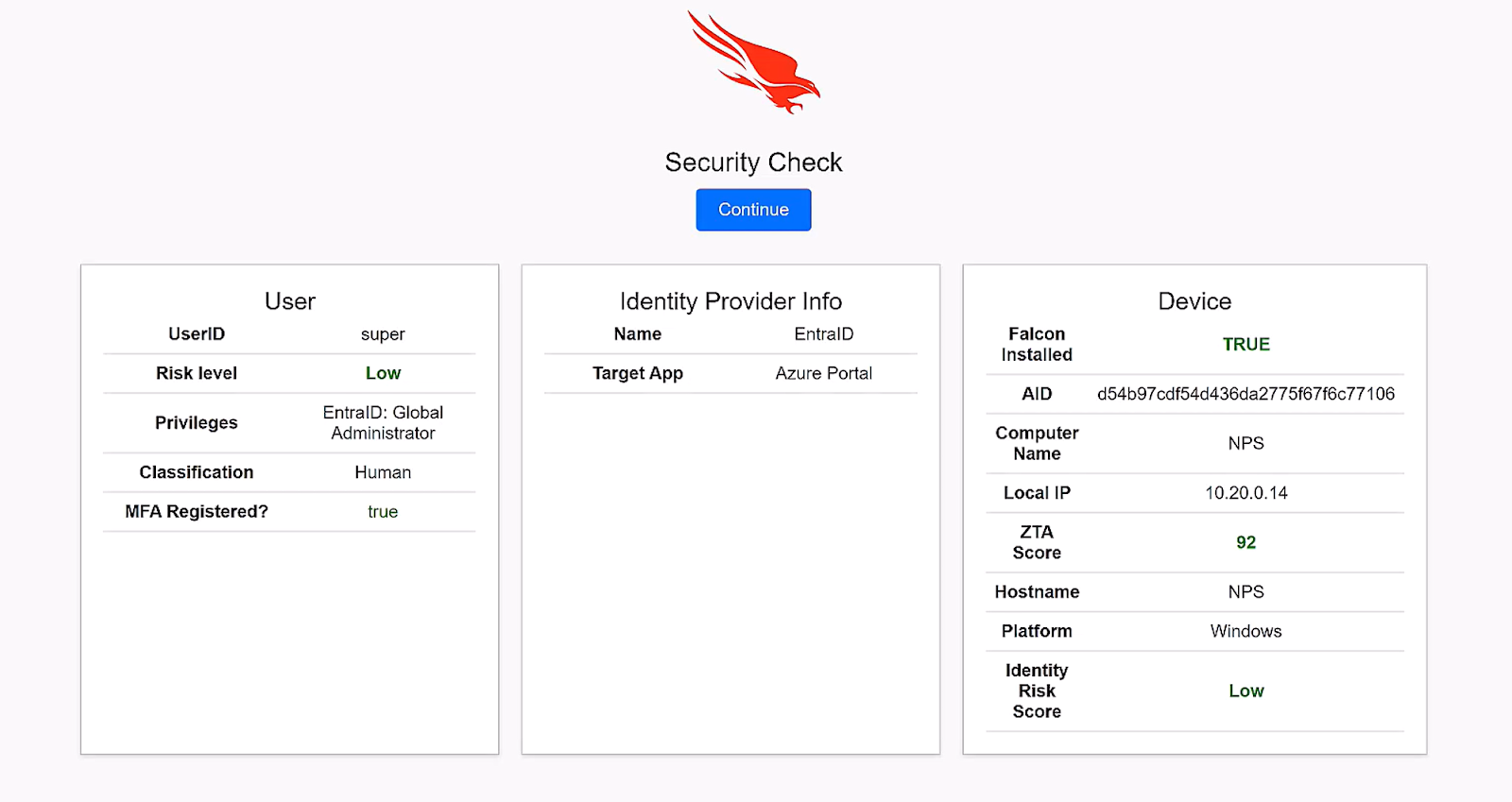
With this integration, Falcon Identity Protection sits inline with the Entra ID flow, acting as the trust point that conducts a security check — factoring user risk, privilege status and more — before granting, blocking or enforcing conditional access.

